CVE-2025-33244
NVIDIA APEX Deserialization Vulnerability
Description
NVIDIA APEX for Linux contains a vulnerability where an unauthorized attacker could cause a deserialization of untrusted data. This vulnerability affects environments that use PyTorch versions earlier than 2.6. A successful exploit of this vulnerability might lead to code execution, denial of service, escalation of privileges, data tampering, and information disclosure.
INFO
Published Date :
March 24, 2026, 9:16 p.m.
Last Modified :
March 25, 2026, 3:41 p.m.
Remotely Exploit :
No
Source :
[email protected]
CVSS Scores
| Score | Version | Severity | Vector | Exploitability Score | Impact Score | Source |
|---|---|---|---|---|---|---|
| CVSS 3.1 | CRITICAL | 9576f279-3576-44b5-a4af-b9a8644b2de6 | ||||
| CVSS 3.1 | CRITICAL | [email protected] |
Solution
- Update PyTorch to version 2.6 or later.
- Avoid deserializing untrusted data.
- Validate all data sources.
- Apply vendor patches when available.
Public PoC/Exploit Available at Github
CVE-2025-33244 has a 1 public
PoC/Exploit available at Github.
Go to the Public Exploits tab to see the list.
References to Advisories, Solutions, and Tools
Here, you will find a curated list of external links that provide in-depth
information, practical solutions, and valuable tools related to
CVE-2025-33244.
| URL | Resource |
|---|---|
| https://nvd.nist.gov/vuln/detail/CVE-2025-33244 | |
| https://nvidia.custhelp.com/app/answers/detail/a_id/5782 | |
| https://www.cve.org/CVERecord?id=CVE-2025-33244 |
CWE - Common Weakness Enumeration
While CVE identifies
specific instances of vulnerabilities, CWE categorizes the common flaws or
weaknesses that can lead to vulnerabilities. CVE-2025-33244 is
associated with the following CWEs:
Common Attack Pattern Enumeration and Classification (CAPEC)
Common Attack Pattern Enumeration and Classification
(CAPEC)
stores attack patterns, which are descriptions of the common attributes and
approaches employed by adversaries to exploit the CVE-2025-33244
weaknesses.
We scan GitHub repositories to detect new proof-of-concept exploits. Following list is a collection of public exploits and proof-of-concepts, which have been published on GitHub (sorted by the most recently updated).
Curated knowledge base tracking pickle deserialization vulnerabilities in ML frameworks. For GRC professionals and security teams.
Python
Results are limited to the first 15 repositories due to potential performance issues.
The following list is the news that have been mention
CVE-2025-33244 vulnerability anywhere in the article.

-
Daily CyberSecurity
Critical 9.8 RCE Threat to SGLang AI Infrastructure
A critical remote code execution (RCE) vulnerability has been uncovered in SGLang, a popular open-source framework used to serve advanced models like DeepSeek and Mistral. The flaw, officially tracked ... Read more
-
Daily CyberSecurity
CVE-2026-34838 (CVSS 10): Critical RCE Flaw Uncovered in GroupOffice CRM
In a significant discovery for enterprises and public sector organizations, a critical security vulnerability has been unmasked in GroupOffice, the popular open-source CRM and groupware suite. The fla ... Read more

-
Daily CyberSecurity
NVIDIA Patches High-Severity “Insecure Deserialization” Flaws in BioNeMo Framework
NVIDIA has issued an important security update for its BioNeMo Framework, a critical tool used by researchers and developers in the generative AI and drug discovery space. The update addresses two hig ... Read more
-
Daily CyberSecurity
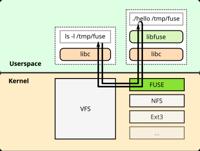
Critical libfuse io_uring Vulnerabilities Threaten Linux and Kubernetes Infrastructure
The FUSE (Filesystem in Userspace) project, a staple of the Linux ecosystem that allows non-privileged users to create their own file systems, is facing a dual-threat. Researchers have identified two ... Read more

-
CybersecurityNews
Critical NVIDIA Vulnerabilities Enables RCE and DoS Attacks
Critical March 2026 security updates have been released to fix multiple vulnerabilities across enterprise and AI software systems. The latest advisories highlight severe flaws that could enable attack ... Read more

-
Daily CyberSecurity
AI Infrastructure at Risk: NVIDIA Fixes Critical 9.0 RCE Flaw in Apex Library (CVE-2025-33244)
NVIDIA has issued an urgent security update for its Apex library to remediate a critical vulnerability that could allow attackers to execute malicious code on Linux-based systems. The flaw, tracked as ... Read more
The following table lists the changes that have been made to the
CVE-2025-33244 vulnerability over time.
Vulnerability history details can be useful for understanding the evolution of a vulnerability, and for identifying the most recent changes that may impact the vulnerability's severity, exploitability, or other characteristics.
-
New CVE Received by [email protected]
Mar. 24, 2026
Action Type Old Value New Value Added Description NVIDIA APEX for Linux contains a vulnerability where an unauthorized attacker could cause a deserialization of untrusted data. This vulnerability affects environments that use PyTorch versions earlier than 2.6. A successful exploit of this vulnerability might lead to code execution, denial of service, escalation of privileges, data tampering, and information disclosure. Added CVSS V3.1 AV:A/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H Added CWE CWE-502 Added Reference https://nvd.nist.gov/vuln/detail/CVE-2025-33244 Added Reference https://nvidia.custhelp.com/app/answers/detail/a_id/5782 Added Reference https://www.cve.org/CVERecord?id=CVE-2025-33244